Enterprise Network Redesign and Security Validation
Masterschool AI Cybersecurity Analyst Track
Project Context and Real-World Considerations
This project was built to the specific requirements of a simulated client engagement and assessed against a defined set of scoring criteria. A reader with real-world engineering experience will recognise some deliberate simplifications, which I want to address directly.
- Headcount and subnet sizing: The 92-employee figure represents the firm's projected headcount, not a ceiling. In a real deployment, subnets would be sized with meaningful growth headroom to avoid costly re-addressing.
- Lab subnets: The virtual lab uses /24 across all VLANs for simplicity. Production uses correctly-sized subnets (/26, /27). This is a documented simplification and does not affect isolation testing validity.
- Single Hyper-V server: Retaining the existing host was the right cost decision for this engagement. In a greenfield design, HA clustering would be the starting point, not an afterthought.
- OPNsense in the lab: OPNsense CE is a functionally equivalent substitute for the FortiGate 100F. Both are stateful firewall platforms with the same policy model. The substitution is documented in Segment 2.
Project Overview
This four-segment capstone project simulates the full lifecycle of a cybersecurity engagement for a midsize professional services firm: from stakeholder-driven network design through hands-on attack execution and SIEM validation. It is not a theoretical exercise. Every design decision was justified against real budget constraints and stakeholder priorities, every firewall rule was tested in a live virtual lab, every attack was executed and captured in a SIEM, and every vulnerability finding was remediated and verified with a post-fix scan. The project covers network architecture, firewall policy, threat modelling, SOC operations planning, penetration testing methodology, and vulnerability management in one connected body of work.
The Brief
The Problem
A midsize professional services firm with 92 employees had a flat, undersegmented network. 58 remote workers, corporate endpoints, finance and HR systems, VoIP phones, IoT devices, and a growing guest WiFi footprint all sharing the same trust boundary.
The Constraints
- CapEx: €25,000 – €45,000
- OpEx ceiling: €1,200 – €4,200 / month
- Existing FortiGate 100F and Hyper-V server retained
- 5 stakeholders with competing priorities
- Governing framework: NIST CSF v2.0
Stakeholders
The Four Segments
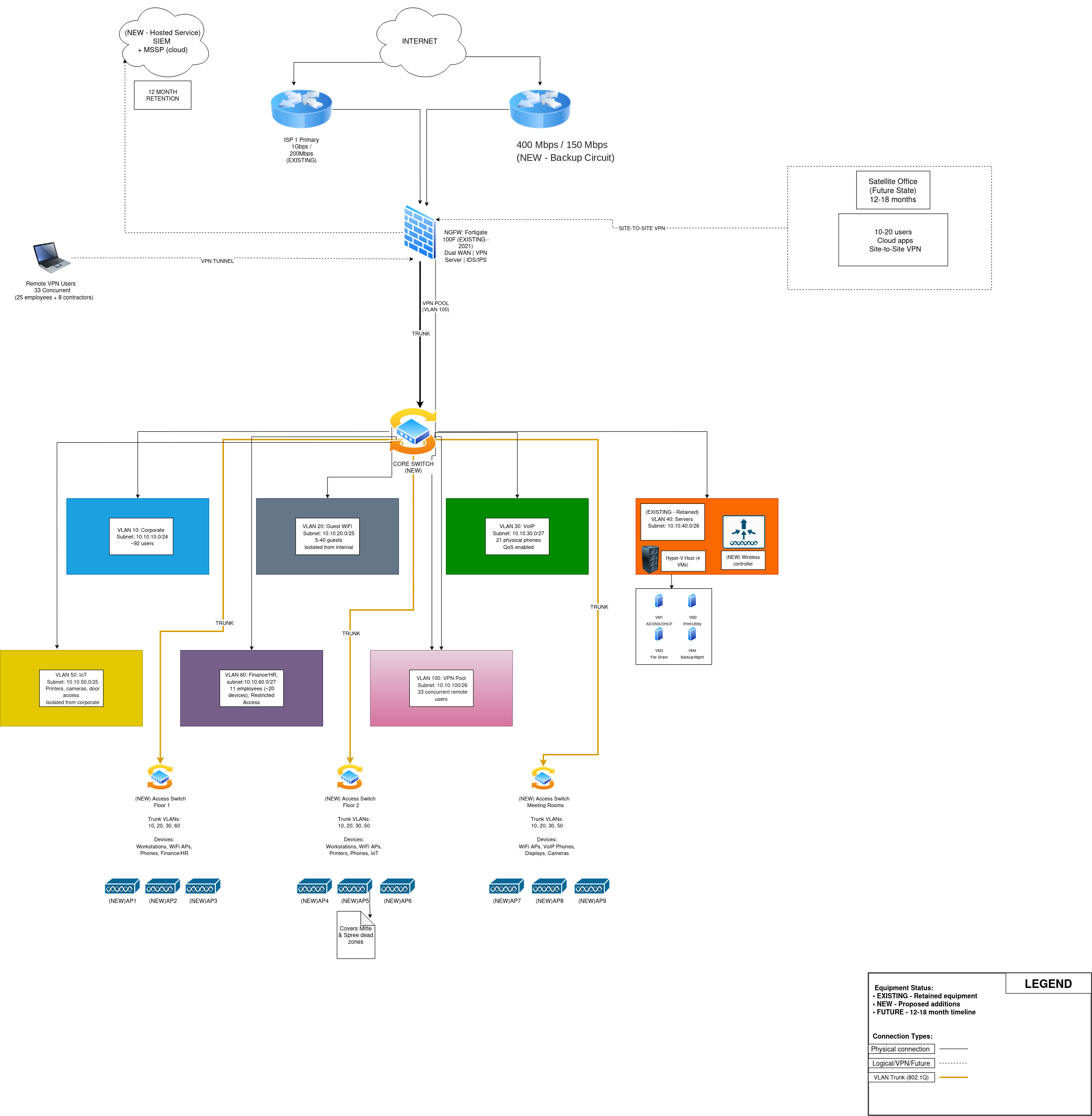
Network Redesign Proposal
The task
Design a segmented network architecture that addresses the firm's risk posture, fits the budget, and survives scrutiny from five stakeholders with different priorities.
Four rounds of stakeholder interviews before finalising the design. The submitted proposal ran 11 pages and received the panel comment: “Approved (Option A). The most real-world signable draft produced.”
| VLAN | Name | Subnet | Notes |
|---|---|---|---|
| 10 | Corporate | 10.10.10.0/24 | ~165 devices |
| 20 | Guest | 10.10.20.0/25 | Internet-only, no lateral access |
| 30 | VoIP | 10.10.30.0/27 | 21 phones, QoS DSCP EF |
| 40 | Servers | 10.10.40.0/26 | Static IPs, AD/DNS/DHCP/File/Print/Backup |
| 50 | IoT | 10.10.50.0/25 | ~50 devices, strict egress policy |
| 60 | Finance/HR | 10.10.60.0/27 | ~20 devices, allow-list only, MFA required |
| 100 | VPN Pool | 10.10.100.0/26 | 33 concurrent sessions at peak |
Virtual Lab Build
The task
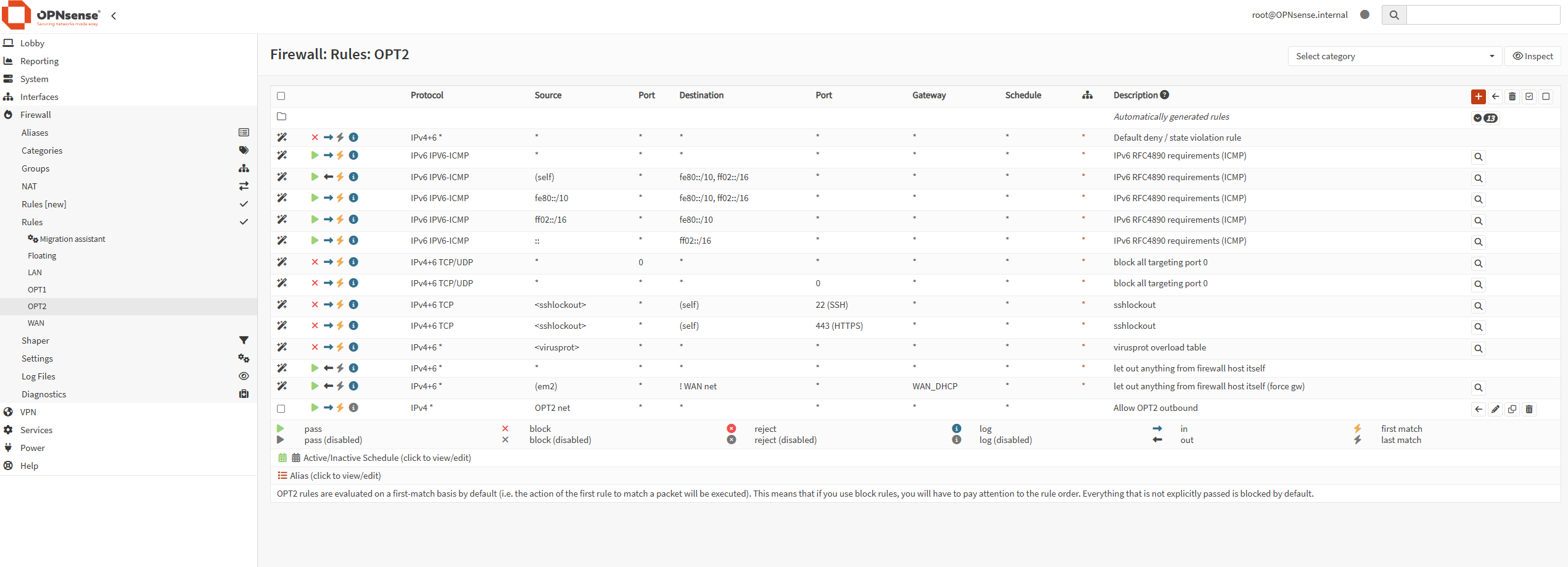
Build a proof-of-concept lab that validates the Segment 1 architecture, demonstrates VLAN isolation, and produces verifiable evidence. VMware Workstation Pro on Windows 11, 64GB RAM. Default-deny firewall policy mirroring the production FortiGate design.
Evidence collected: DHCP lease screenshots from all three VLANs, firewall rule exports, ping and traceroute from every VM confirming correct routing and blocking, and three packet captures. Every lab component is mapped to its production equivalent in an alignment section.
Security and SOC Plan
The task
Produce a formal 12-page security document covering threat modelling, firewall policy, device hardening, logging, SOC operations, incident response playbooks, and a seven-phase deployment roadmap. Structured around NIST CSF v2.0. Seven threats scored on a 5x5 Likelihood x Impact matrix (STRIDE-categorised).
| ID | Threat | Score | Rating |
|---|---|---|---|
| T-01 | Ransomware via phishing to VLAN 40 | 25 | CRITICAL |
| T-02 | VPN credential compromise | 16 | HIGH |
| T-03 | Insider threat / Finance-HR exfiltration | 15 | HIGH |
| T-04 | IoT firmware exploit pivot | 12 | MEDIUM |
| T-05 | DoS against primary ISP | 12 | MEDIUM |
| T-06 | Guest WiFi VLAN hopping | 8 | MEDIUM |
| T-07 | Supply chain firmware compromise | 5 | LOW |
Three full incident response playbooks following NIST SP 800-61: Ransomware (RTO 4h, RPO 24h, GDPR 72h notification window), VPN Credential Compromise, and Insider Threat / Finance-HR Exfiltration. SOC model with four roles and SLA-based escalation paths.
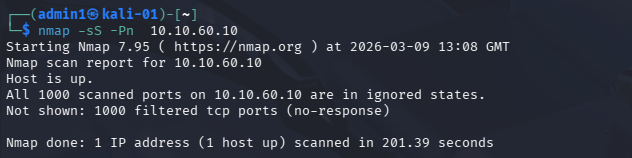
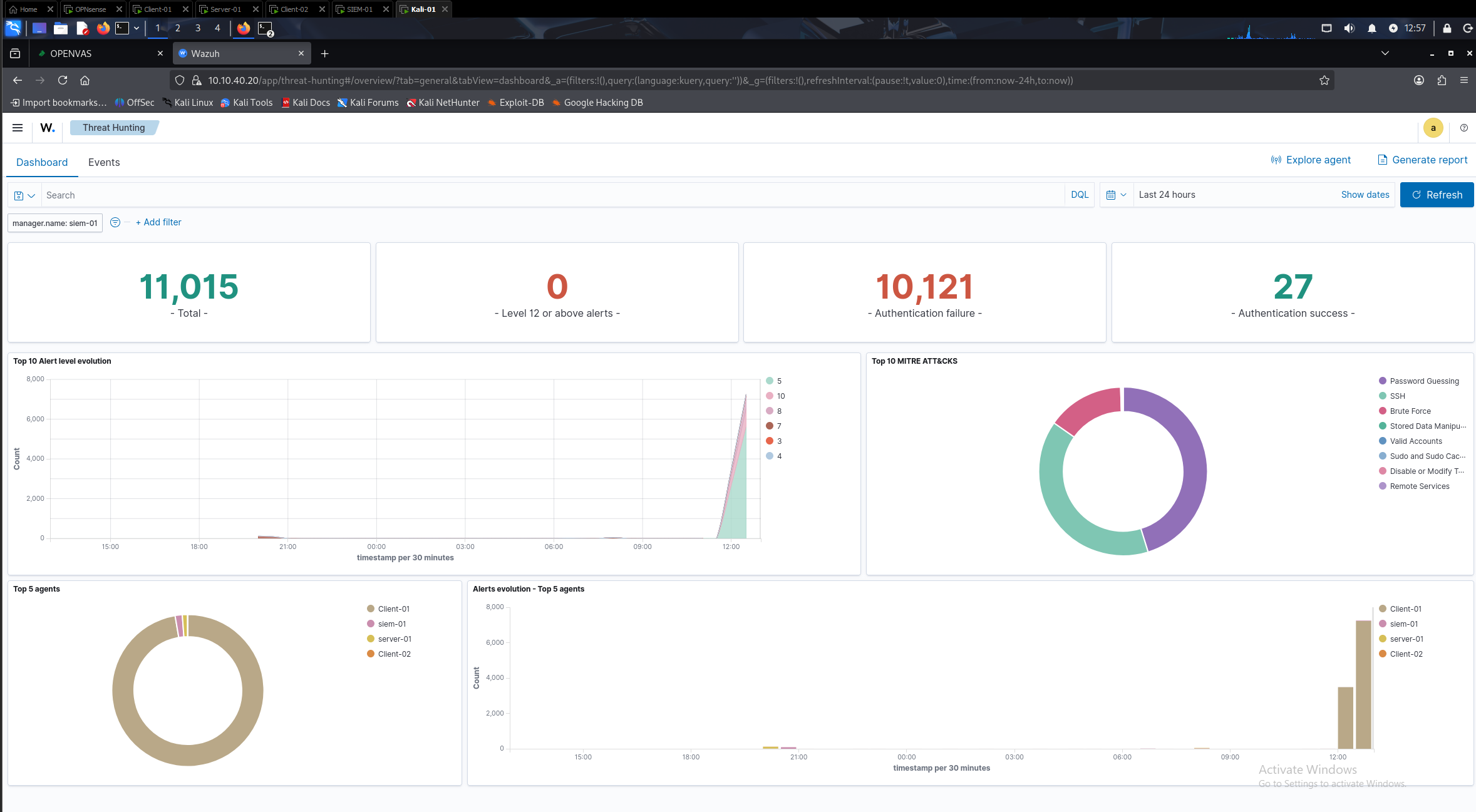
Security Validation
The task
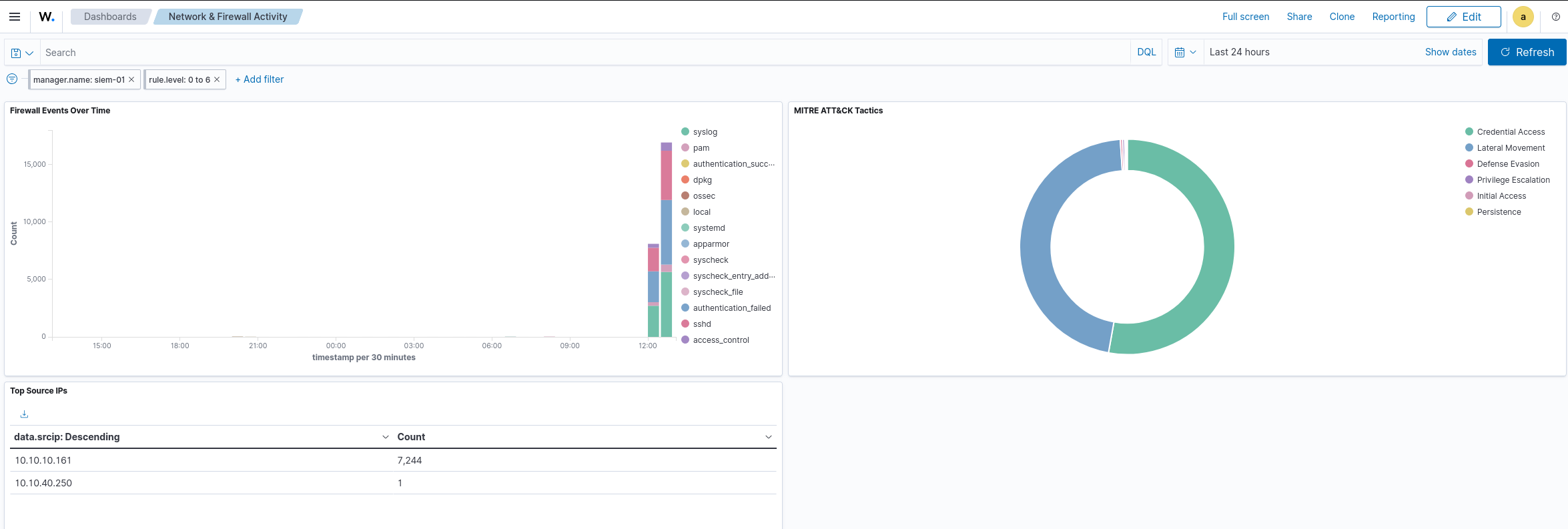
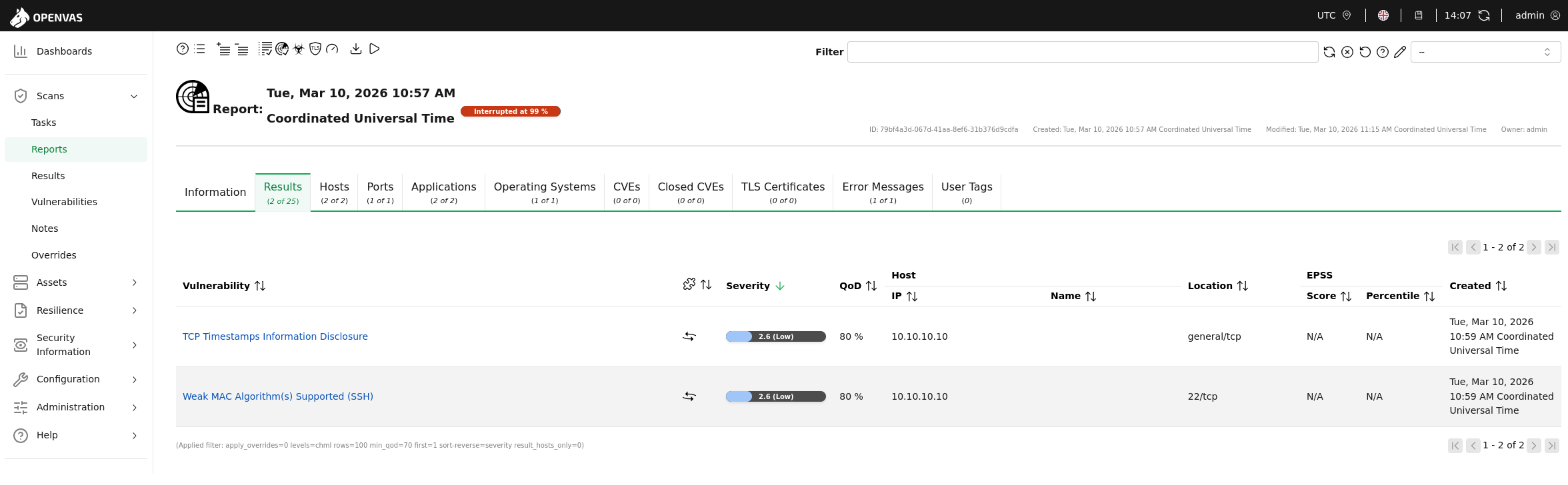
Extend the lab with attack infrastructure and a SIEM. Execute real attacks, validate that detections fire, run a vulnerability scan, remediate findings, and verify the fixes with a post-fix scan.
Technical Challenges
Honest documentation of problems and how they were resolved is part of the work.
pfSense WAN failure
pfSense could not establish WAN connectivity in VMware. Diagnosed, documented, and substituted with OPNsense CE — recorded in the Segment 2 submission rather than omitted.
FreeBSD NIC enumeration
OPNsense (FreeBSD) enumerates network interfaces in a different order than VMware presents adapters. Resolved by assigning interfaces via MAC address comparison.
VMware host adapter IP conflict
vmnet11 host adapter (10.10.40.1) collided with OPNsense's OPT1 gateway, breaking inter-VLAN routing via ARP. Fixed by reassigning the host adapter to 10.10.40.250.
Wazuh syslog not appearing
OPNsense syslog traffic confirmed arriving via tcpdump, but not appearing in Wazuh. Root cause: remoted daemon not configured for external syslog on UDP 514. Fixed in ossec.conf.
GVM disk fill
GVM PostgreSQL database grew to 19GB and filled the disk to 100%. Recovery: pg_dropcluster, pg_createcluster, and full gvm-setup rebuild.
Wazuh CVE database fill
Wazuh vulnerability detection downloaded 12.7GB of CVE data and filled the 24GB disk. Fixed by extending the LVM volume to 48GB and disabling the vulnerability-detection module.
Skills and Tools Demonstrated
Networking
Firewall and Security Policy
Virtualisation
Operating Systems
SIEM
Attack Tools
Vulnerability Management
Hardening
Frameworks
Documentation
Closing
This project represents the full scope of a junior-to-mid security practitioner's responsibility on a real engagement: understanding business requirements, translating them into a technical design, building and testing that design in a controlled environment, planning and operating a detection capability, and proving it works under adversarial conditions. The work is grounded in constraints that exist in real organisations, not clean-room assumptions. Every major decision has a documented reason, and every claimed outcome has evidence behind it.
The capstone deliberately mirrors what entry-level and mid-level security roles actually involve: a mix of architecture, operations, analysis, and communication. That breadth is intentional, and the depth within each segment demonstrates that the breadth is not superficial.